Numerous cybercriminal improvements are making it simpler for scammers to money in in your upcoming journey plans. This story examines a current spear-phishing marketing campaign that ensued when a California resort had its reserving.com credentials stolen. We’ll additionally discover an array of cybercrime companies aimed toward phishers who goal resorts that depend on the world’s most visited journey web site.
In accordance with the market share web site statista.com, reserving.com is by far the Web’s busiest journey service, with almost 550 million visits in September. KrebsOnSecurity final week heard from a reader whose shut buddy acquired a focused phishing message throughout the Reserving cell app simply minutes after making a reservation at a California.
The missive bore the title of the resort and referenced particulars from their reservation, claiming that reserving.com’s anti-fraud system required further details about the shopper earlier than the reservation might be finalized.
The phishing message our reader’s buddy acquired after making a reservation at reserving.com in late October.
In an e-mail to KrebsOnSecurity, reserving.com confirmed one among its companions had suffered a safety incident that allowed unauthorized entry to buyer reserving info.
“Our safety groups are at the moment investigating the incident you talked about and might verify that it was certainly a phishing assault concentrating on one among our lodging companions, which sadly is just not a brand new state of affairs and fairly frequent throughout industries,” reserving.com replied. “Importantly, we need to make clear that there was no compromise of Reserving.com’s inner programs.”
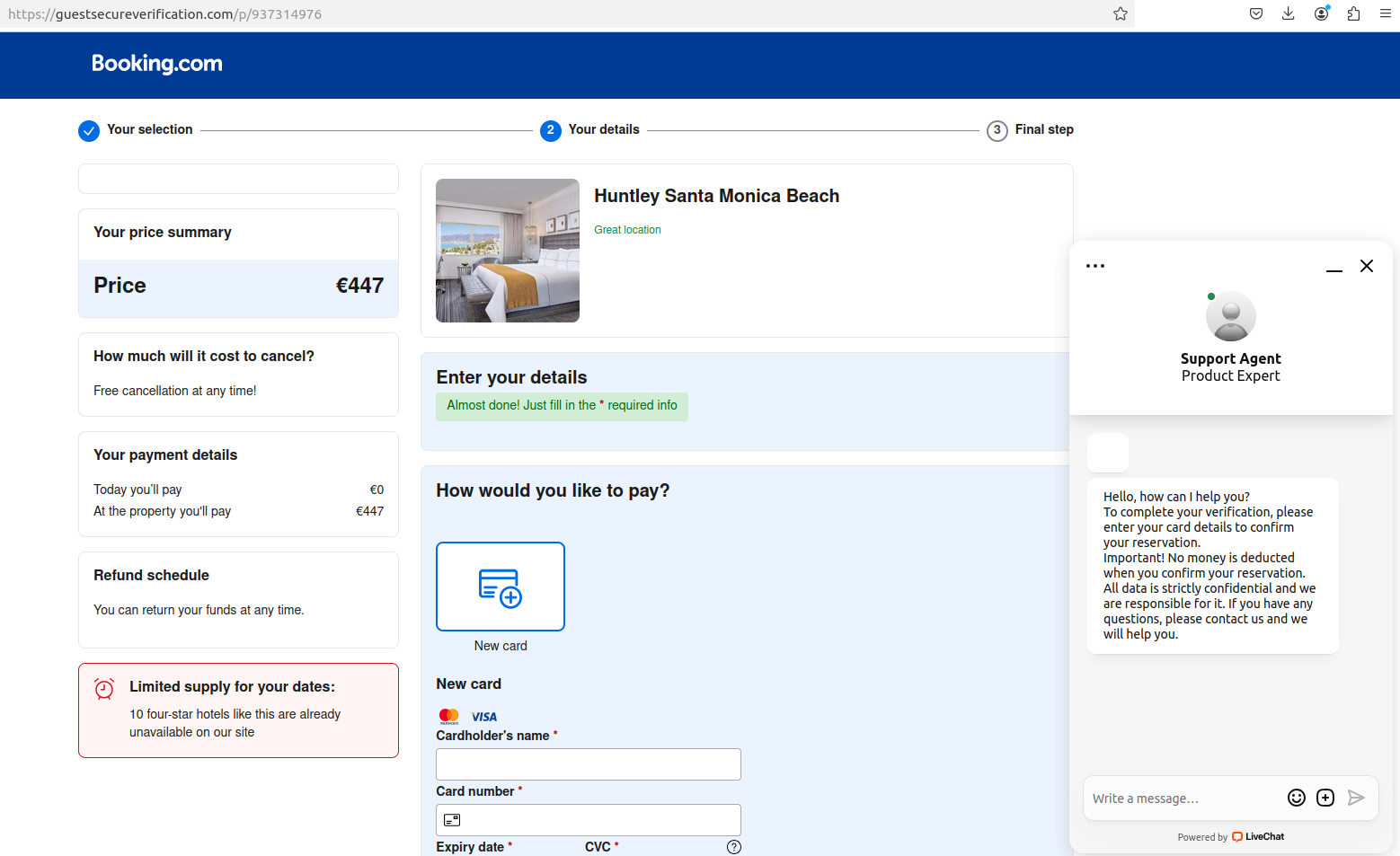
The phony reserving.com web site generated by visiting the hyperlink within the textual content message.
Reserving.com mentioned it now requires 2FA, which forces companions to offer a one-time passcode from a cell authentication app (Pulse) along with a username and password.
“2FA is required and enforced, together with for companions to entry fee particulars from prospects securely,” a reserving.com spokesperson wrote. “That’s why the cybercriminals follow-up with messages to try to get prospects to make funds exterior of our platform.”
“That mentioned, the phishing assaults stem from companions’ machines being compromised with malware, which has enabled them to additionally acquire entry to the companions’ accounts and to ship the messages that your reader has flagged,” they continued.
It’s unclear, nonetheless, if the corporate’s 2FA requirement is enforced for all or simply newer companions. Reserving.com didn’t reply to questions on that, and its present account safety recommendation urges prospects to allow 2FA.
A scan of social media networks confirmed this isn’t an unusual rip-off.
In November 2023, the safety agency SecureWorks detailed how scammers focused reserving.com hospitality companions with data-stealing malware. SecureWorks mentioned these assaults had been occurring since at the least March 2023.
“The resort didn’t allow multi-factor authentication (MFA) on its Reserving.com entry, so logging into the account with the stolen credentials was straightforward,” SecureWorks mentioned of the reserving.com companion it investigated.
In June 2024, reserving.com instructed the BBC that phishing assaults concentrating on vacationers had elevated 900 %, and that thieves benefiting from new synthetic intelligence (AI) instruments had been the first driver of this development.
Reserving.com instructed the BCC the corporate had began utilizing AI to battle AI-based phishing assaults. Reserving.com’s assertion mentioned their investments in that enviornment “blocked 85 million fraudulent reservations over greater than 1.5 million phishing makes an attempt in 2023.”
The area title within the phony reserving.com web site despatched to our reader’s buddy — guestssecureverification[.]com — was registered to the e-mail deal with ilotirabec207@gmail.com. In accordance with DomainTools.com, this e-mail deal with was used to register greater than 700 different phishing domains up to now month alone.
Lots of the 700+ domains seem to focus on hospitality firms, together with platforms like reserving.com and Airbnb. Others appear crafted to phish customers of Shopify, Steam, and a wide range of monetary platforms. A full, defanged record of domains is offered right here.
A cursory evaluate of current posts throughout dozens of cybercrime boards monitored by the safety agency Intel 471 exhibits there’s a nice demand for compromised reserving.com accounts belonging to resorts and different companions.
One publish final month on the Russian-language hacking discussion board BHF supplied as much as $5,000 for every resort account. This vendor claims to assist folks monetize hacked reserving.com companions, apparently by utilizing the stolen credentials to arrange fraudulent listings.
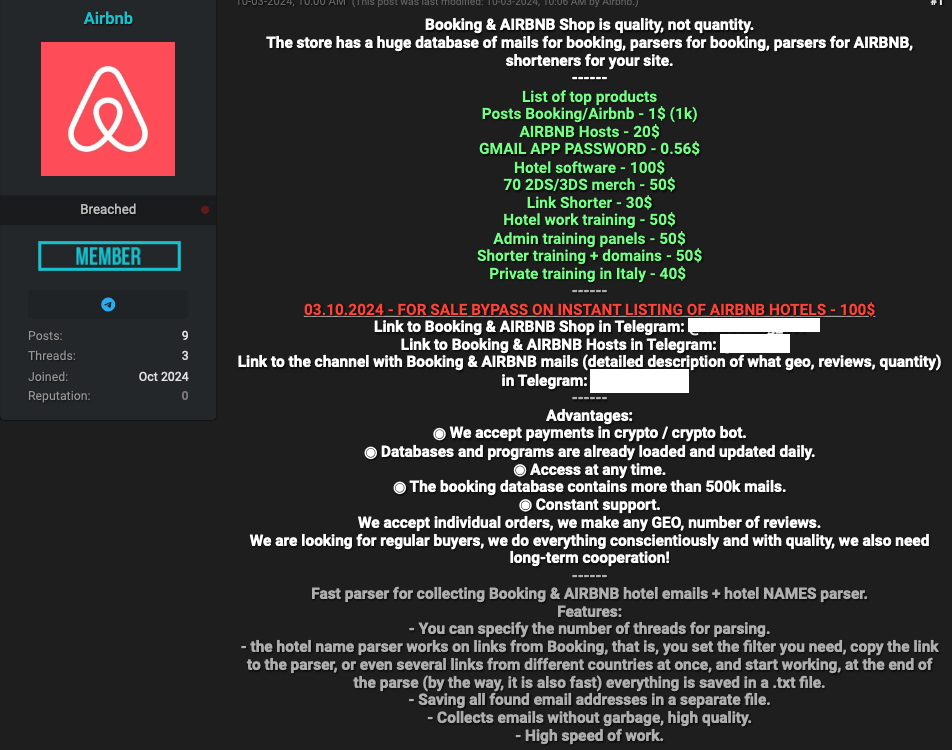
A service marketed on the English-language crime group BreachForums in October courts phishers who might need assistance with sure elements of their phishing campaigns concentrating on reserving.com companions. These embrace greater than two million resort e-mail addresses, and companies designed to assist phishers set up massive volumes of phished data. Clients can work together with the service by way of an automatic Telegram bot.
Some cybercriminals seem to have used compromised reserving.com accounts to energy their very own journey companies catering to fellow scammers, with as much as 50 % reductions on resort reservations by means of reserving.com. Others are promoting ready-to-use “config” information designed to make it easy to conduct automated login makes an attempt in opposition to reserving.com administrator accounts.
SecureWorks discovered the phishers concentrating on reserving.com companion resorts used malware to steal credentials. However at this time’s thieves can simply as simply simply go to crime bazaars on-line and buy stolen credentials to cloud companies that don’t implement 2FA for all accounts.
That’s precisely what transpired over the previous yr with many purchasers of the cloud knowledge storage big Snowflake. In late 2023, cybercriminals discovered that whereas tons of firms had stashed huge quantities of buyer knowledge at Snowflake, a lot of these buyer accounts weren’t protected by 2FA.
Snowflake responded by making 2FA obligatory for all new prospects. However that change got here solely after thieves used stolen credentials to siphon knowledge from 160 firms — together with AT&T, Lending Tree and TicketMaster.

